In the rapidly evolving landscape of Ethereum, EIP-7702 session keys emerge as a game-changer for AI agents ERC-4337 integration, unlocking true smart wallet task automation. Imagine your wallet not just holding assets, but intelligently executing trades, staking, or DeFi strategies on autopilot, all while you sleep. This isn't science fiction; it's the promise of combining account abstraction advancements with session keys, allowing EOAs to borrow smart contract powers temporarily. As someone who's watched markets cycle through booms and busts, I see this as the patient observer's edge: secure, scalable automation that hedges against human error in blockchain's volatile arena.
This synergy isn't rivalry; it's complementary. ERC-4337 handles the infrastructure, while EIP-7702 democratizes access. Developers gain backward compatibility, users retain their addresses, and the network scales without address churn.
Session Keys: The Backbone of Granular Permissions
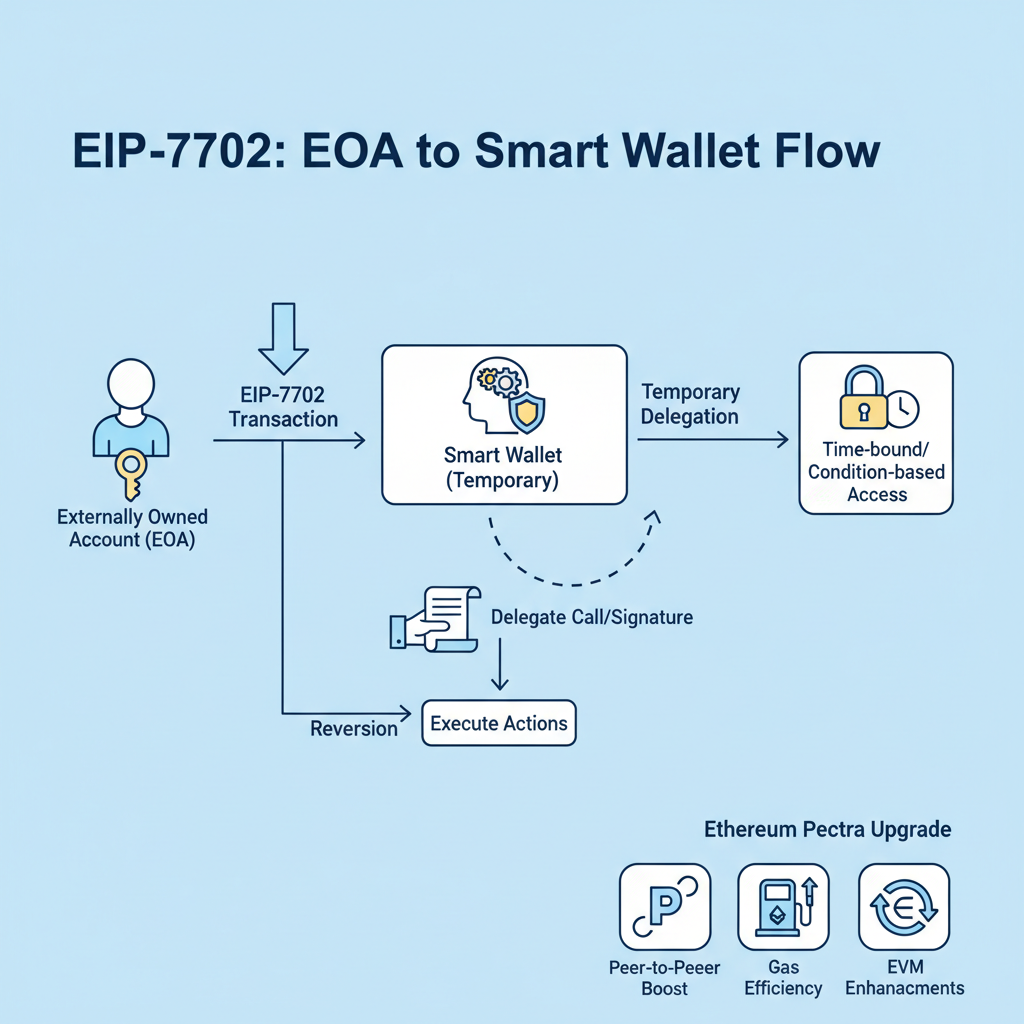
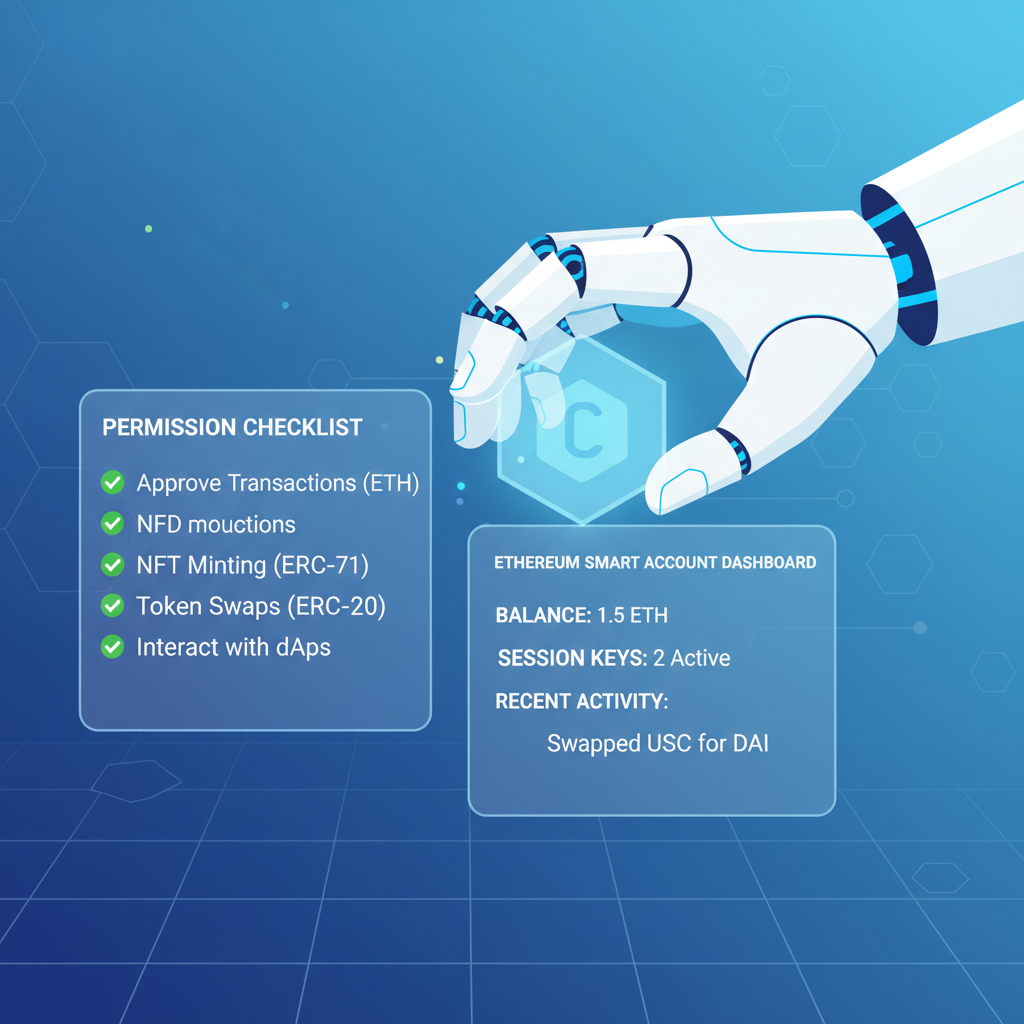
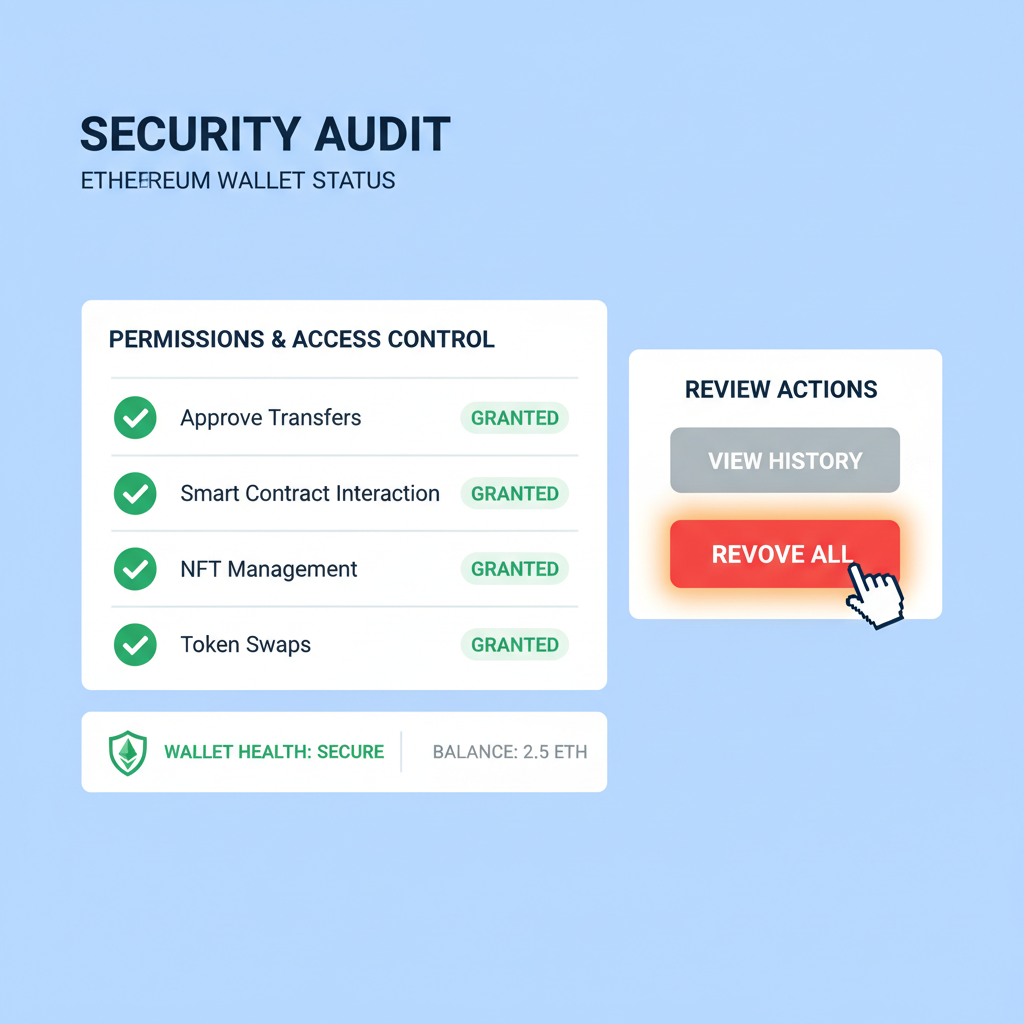
At the heart of blockchain AI automation lie session keys, ephemeral permissions that smart accounts issue to agents or dApps. Under ERC-4337, a session key might allow an AI to approve a swap up to $1,000 daily, valid for 24 hours, without touching your main private key. EIP-7702 supercharges this: EOAs can now issue these keys too, turning vanilla wallets into permissioned powerhouses.
Think methodically about security. Traditional multisig is clunky for automation; session keys are surgical. Built on standards like ERC-7579, they encode rules: time-bound, value-capped, contract-specific. Rhinestone's Smart Sessions exemplify this, modular hooks for validators and executors. For AI agents, this means delegated tasks like yield farming across protocols, auto-compounding rewards, all audited and revocable in one UserOp.
I've long advocated long-term holds, but automation demands trustless execution. Session keys deliver: no full custody, just scoped authority. In practice, an AI agent could monitor macro signals - say, bond yields spiking - and rebalance your portfolio via EIP-7702 session keys, sponsoring its own gas if needed.
AI Agents Unleashed: Automating Tasks in Smart Wallets[/h2>
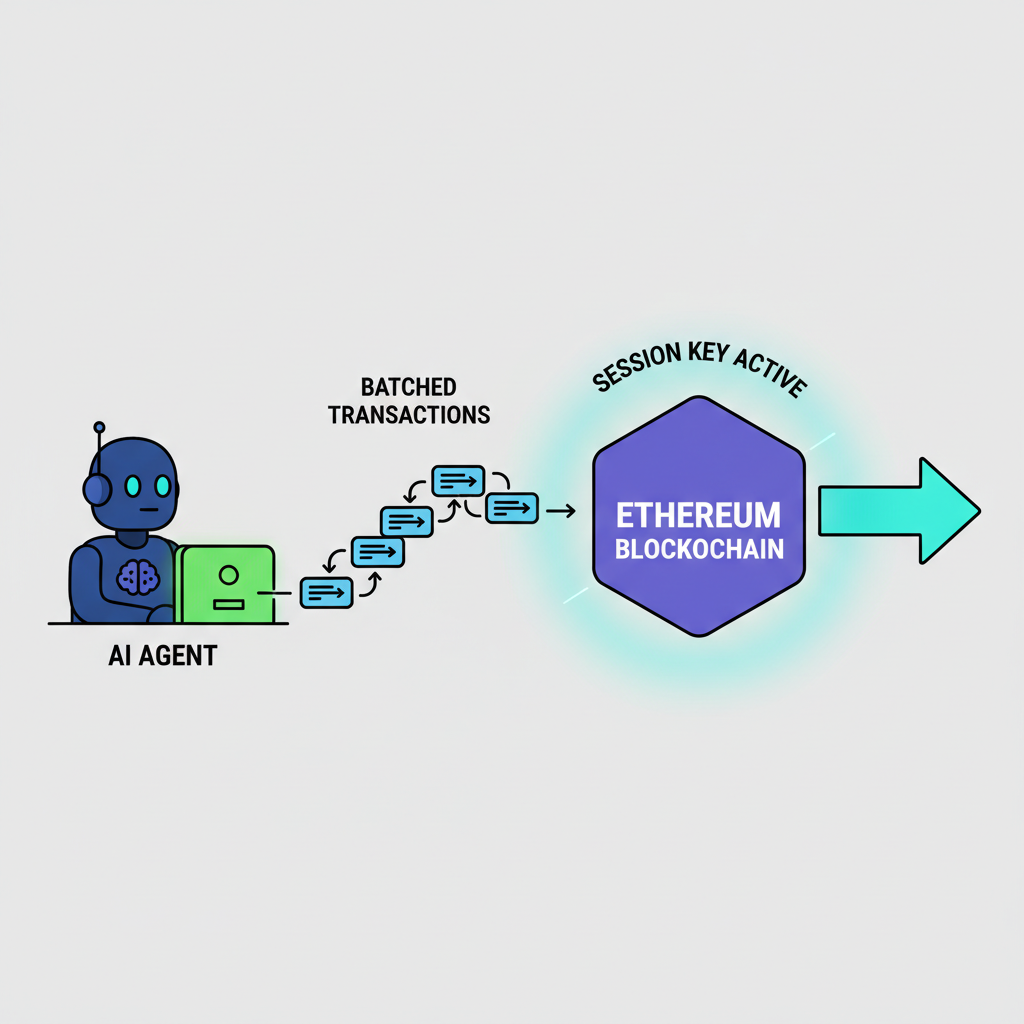
Now, fuse these with AI agents, and smart wallet task automation hits escape velocity. Picture an agent powered by EIP-7702: it ingests on-chain data, runs off-chain inference, then submits UserOps via session keys. No seed phrase risks; just temporary delegation. For instance, in DeFi, agents batch liquidations, arbitrages, or NFT mints, optimizing across chains if L2s adopt.
Platforms like SmartAgentKeys. com pioneer this, leveraging EIP-7702 for keyless interactions. Developers implement hooks for AI logic: predict volatility, execute hedges. Users grant sessions via simple signatures, revocable anytime. This isn't hype; it's methodical progress. ERC-4337 provides the bundler-paymaster duo, EIP-7702 the EOA gateway, session keys the AI leash.
Consider real-world flows. An institutional trader delegates an agent for commodities-linked tokens, inflation hedges I favor. The agent watches ETH/BTC ratios, auto-buys dips under session limits. Secure, efficient, patient - markets reward such observers.
Granular control like this transforms passive holding into active, yet secure, management. But how does it work under the hood? Let's break it down methodically for developers eyeing account abstraction session keys.
Developer Guide: Wiring EIP-7702 Session Keys for AI Agents
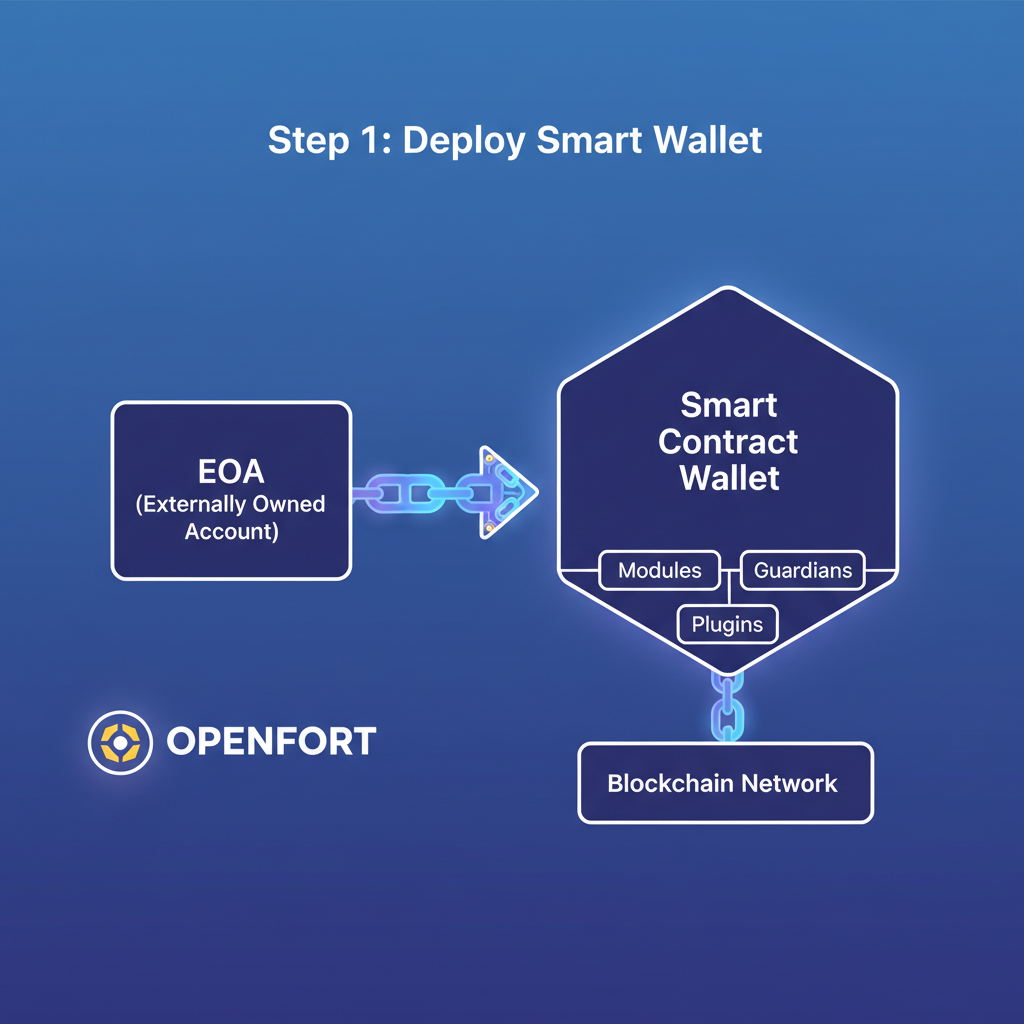
Implementation starts with understanding the AUTH transaction type in EIP-7702. An EOA signs a delegation to a smart contract code, temporarily adopting its logic for one transaction. Pair this with ERC-4337's UserOperation, and you bundle session key validations into paymaster-sponsored ops. The flow: user signs session key params (limits, expiry, targets), AI agent uses it to call execute() on the account, EntryPoint verifies, bundles, and broadcasts.
For ERC-4337 natives, extend your smart account with ERC-6900 modules or ERC-7579 hooks. Rhinestone. dev's Smart Sessions offer plug-and-play: define validators for value, time, nonce. EIP-7702 adds the EOA bridge, no migration needed. Tools like MetaMask's Smart Accounts Kit simplify bundling; Openfort handles deployment-on-the-fly.
Session Key Validation Hook in ERC-4337 Smart Account
To enable secure AI agent task automation, ERC-4337 smart accounts can incorporate session key validation hooks compatible with EIP-7702 delegations. This methodical approach verifies each UserOperation step-by-step: confirming the signer is a registered session key, checking expiry, enforcing value caps on transfers, and restricting actions to a whitelisted set of targets. The example below demonstrates this in a minimal smart account implementation.
```solidity
// SPDX-License-Identifier: MIT
pragma solidity ^0.8.20;
import {IAccount} from "@account-abstraction/interfaces/IAccount.sol";
import {PackedUserOperation} from "@account-abstraction/interfaces/PackedUserOperation.sol";
import {EntryPoint} from "@account-abstraction/core/EntryPoint.sol";
/// @title SessionKeyAccount - ERC-4337 Smart Account with EIP-7702 Session Key Support
/// @notice Implements session key validation with value cap, expiry, and target whitelist
contract SessionKeyAccount is IAccount {
EntryPoint private constant EP = EntryPoint(0x5FF137D4b0FDCD49DcA30c7CF57E578a026d2789);
struct SessionKeyPermissions {
uint256 valueCap;
uint256 expiry;
mapping(address => bool) targetWhitelist;
}
mapping(address => SessionKeyPermissions) public sessionKeys;
/// @notice Setup a new session key with permissions
/// @dev Called during initialization or via owner
function setupSessionKey(address sessionKey, uint256 valueCap, uint256 expiry, address[] calldata targets) external {
// Assume owner-only modifier here
SessionKeyPermissions storage perms = sessionKeys[sessionKey];
perms.valueCap = valueCap;
perms.expiry = expiry;
for (uint i = 0; i < targets.length; ++i) {
perms.targetWhitelist[targets[i]] = true;
}
}
function validateUserOp(
PackedUserOperation calldata userOp,
bytes32 userOpHash,
uint256 missingAccountFunds
) external returns (uint256 validationData) {
require(msg.sender == address(EP), "Only EntryPoint");
// Recover signer from signature (simplified; use proper ECDSA recovery)
address signer = _recoverSigner(userOpHash, userOp.signature);
// Check if signer is a registered session key
SessionKeyPermissions storage perms = sessionKeys[signer];
require(perms.expiry >= block.timestamp, "Session key expired");
// Parse callData assuming standard execute(address,uint256,bytes) pattern
require(userOp.callData.length >= 4 + 32*3, "Invalid callData format");
bytes4 selector = bytes4(userOp.callData);
require(selector == bytes4(keccak256("execute(address,uint256,bytes)")), "Invalid execute selector");
address target;
uint256 value;
// solhint-disable-next-line no-inline-assembly
assembly {
target := calldataload(add(userOp.callData.offset, 4))
value := calldataload(add(userOp.callData.offset, 36))
}
require(perms.targetWhitelist[target], "Target not whitelisted");
require(value <= perms.valueCap, "Value exceeds cap");
// EIP-7702 delegation compatibility: additional check if needed for delegated tx
// (e.g., verify authorization list in context; simplified here)
// Return 0 for success (no deadline restriction)
return 0;
}
// Placeholder for signer recovery
function _recoverSigner(bytes32 hash, bytes calldata signature) internal pure returns (address) {
// Implement ECDSA recovery logic here
return address(0);
}
}
```This validation ensures session keys operate within strict boundaries, preventing unauthorized or excessive actions. In a full deployment, integrate proper signature recovery, owner controls for session key setup, and EIP-7702-specific delegation verification from the transaction context. Deploy alongside an EntryPoint contract for ERC-4337 account abstraction.
This snippet illustrates a validator function. Customize predicates: add oracle price checks for macro hedges, or chain ID restrictions for L2s. Test on BuildBear Labs' stacks, mimicking production bundlers.
ERC-4337 and EIP-7702: Complementary Forces
Differences matter, but synergy wins. ERC-4337 mandates smart accounts from inception; EIP-7702 retrofits EOAs. Trade-offs? ERC-4337 scales via bundlers but requires deployment; EIP-7702 skips that, risking code bugs in delegation. Yet together, they cover all bases: new users get full AA, legacy holdouts upgrade seamlessly.
Key Differences and Synergies between ERC-4337 and EIP-7702 for AI Agent Task Automation
| Feature | ERC-4337 | EIP-7702 | Combined Benefit |
|---|---|---|---|
| Deployment | Requires deploying a new smart contract wallet | EOAs temporarily delegate to smart contract code (no new address) | Existing EOAs gain smart features instantly without migration |
| UserOp Bundling | Bundlers aggregate and execute UserOperations | Supports batching via AUTH/AUTHCALL transactions | EIP-7702 txs bundled efficiently in ERC-4337 infrastructure for automation |
| Session Keys | Supported via modular plugins (e.g., ERC-7579) | Enabled for EOAs through temporary delegation | Granular, time-bound permissions for secure AI agent operations |
| EOA Compatibility | Limited; EOAs must migrate to smart accounts | Native support for existing EOAs | Backward-compatible upgrade path without address changes |
| Gas Sponsorship | Via Paymasters in UserOps | Through delegated contracts and compatible Paymasters | Relayer-free sponsorship for AI tasks across both paradigms |
| AI Use Cases | Automated tasks in deployed smart wallets | Temporary permissions for agents without exposing main keys | Secure, scalable AI automation with session keys, bundling, and sponsorship |
As the table highlights, combined benefits shine for AI agents ERC-4337 setups. No more EOA limitations; agents operate across account types.
Security demands scrutiny. Session keys mitigate risks via scopes, but smart contract audits are non-negotiable. I've seen macro cycles wipe out sloppy setups; here, revocability and nonces prevent replays. Gas sponsorship lets agents run lean, vital for frequent tasks like arbitrage.
Real-World Adoption and Hurdles
Adoption accelerates. Turnkey charts ERC-4337's rise, now bolstered by EIP-7702 in Pectra upgrade pipelines. LimeChain notes session keys automating payments; Alchemy contrasts with deprecated EIP-3074, favoring EIP-7702's cleaner delegation. Reddit threads buzz on gas diffs: EIP-7702 cheaper for one-offs, ERC-4337 for complexes.
Challenges persist: bundler centralization, L2 fragmentation. Solutions emerge via decentralized relayers and cross-chain standards. For AI, off-chain compute must trustlessly prove actions; zero-knowledge sessions on horizon.
In my view, this stack hedges inflation beautifully. AI agents auto-allocate to commodities tokens during bond spikes, compounding yields patiently. Platforms like SmartAgentKeys. com lead, offering EIP-7702-powered agents for dApp workflows. Developers, integrate today: fork their repos, deploy testnets, observe the edge.
The patient observer thrives. With EIP-7702 session keys, smart wallets evolve from vaults to vigilant strategists, automating blockchain AI automation without surrendering control. Ethereum's abstraction era rewards those building now.








No comments yet. Be the first to share your thoughts!